
AWS Re: Invent 2021
The Amazon Web Services Re: Invent 2021 event just took place between November 29 and December 3, 2021. This is one of the year's most awaited events. Amazon's AWS has proven to be a cash cow. It has a $64 billion revenue run rate and is growing at a pace of 39% year over year. AWS' growth rate had increased to 39% in 2020 from 29% in 2020. Because of its financial health and the continuous growth of the cloud large enterprise industry as a whole, parent firm Amazon has been able to exert influence in the development of new businesses and upsetting markets.
With these variables in mind, it's no surprise that AWS' event is one of the most awaited of the year. We forecast what will happen during the event based on the release and trends in the cloud market, among other variables.
S3 access Management
AWS has released an update for its Simple Storage Service (S3) that intends to make managing S3 data easier.
Users can deactivate access control lists (ACLs) using a new Amazon S3 Object Owning setting, and the Amazon S3 console policy editor now "reports security warnings, problems, and solutions driven by IAM Access Analyzer as you compose your S3 policies," according to an AWS blog.
The new Bucket owner mandated Amazon S3 Object Ownership setting "allow you deactivate all of the ACLs connected with a bucket and the objects in it," according to the blog. "When you apply this bucket-level configuration, the AWS account that generated the bucket owns all of the objects in the bucket, and ACLs are no longer utilized to give access." Ownership of the bucket changes automatically after it is applied, and applications that write data to it no longer need to define any ACLs.
Automated DDoS mitigation at the application layer
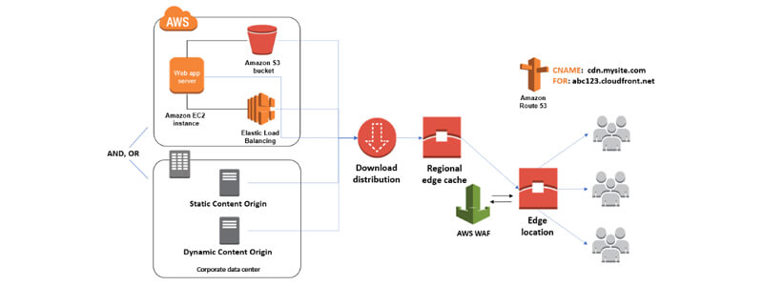
AWS released an update to AWS Shield, the company's dedicated DDoS protection service for apps running on AWS, to assist clients in mitigating distributed denial-of-service (DDoS) attacks.
According to AWS, the latest upgrade adds automatic application-layer DDoS mitigation to AWS Shield Advanced.
In a blog post, the business claimed, "This is a new set of skills provided for all Shield Advanced clients that automatically neutralize harmful web traffic that compromises uptime." "This feature builds, tests, and executes AWS WAF rules on behalf of its customers to mitigate layer 7 DDoS events."
Auditing and Network Access Management
With the Amazon Virtual Private Cloud (VPC) IP Address Manager, AWS introduced network address monitoring and auditing "at scale" (IPAM). "The new capability gives network managers an automated IP management procedure," according to the description. In a blog post, AWS stated that IPAM "makes it a lot easier for network managers to organize, distribute, analyze, and inspect IP addresses in at-scale networks, minimizing the tracking and reporting burden and removing manual operations that can result in delays and inadvertent failures."
Amazon Workspace Web
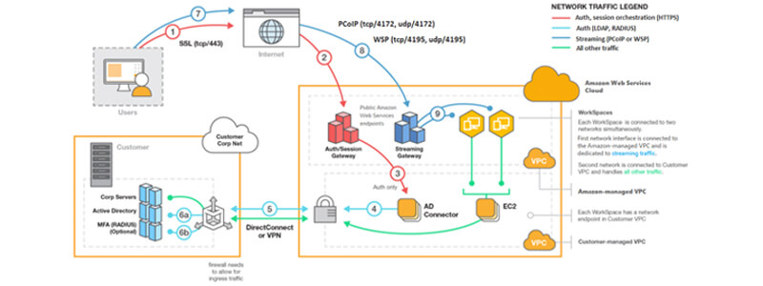
AWS launched the general release of Amazon WorkSpaces Web, a "low cost, managed service WorkSpace created expressly to support safe, web-based workflows," in terms of enabling private end-user computing.
"WorkSpaces Web enables businesses to securely deploy internal websites and SaaS web applications to their workers without the administrative overhead of appliances or dedicated client software," AWS wrote in a blog post. "Corporate data is never stored on distant devices using Amazon WorkSpaces Web." In AWS, websites are rendered in a separate container then pixel broadcast to the user. The separated browsing session acts as a strong defense against web-based assaults and prevents possibly affected end systems from ever connecting to private servers."
"Each session" also "launches a new, always up to current, spatially dispersed web browser." "WorkSpaces Web supports venture controls that allow administrators to set browser guidelines (e.g., set default home page, browsing history, enable/disable extensions, enable list specific URLs or any of Chrome's 300+ policies) and user settings (e.g. clipboard, file transfer, or local printer controls) and preferences menu (e.g., clipboard, data transfer, or local printer controls)," according to the blog. "When the session is finished, the browser instance is stopped, ensuring that sensitive business web material is never outside of the control of the organization."
VPC oriented Network Access Analyzer
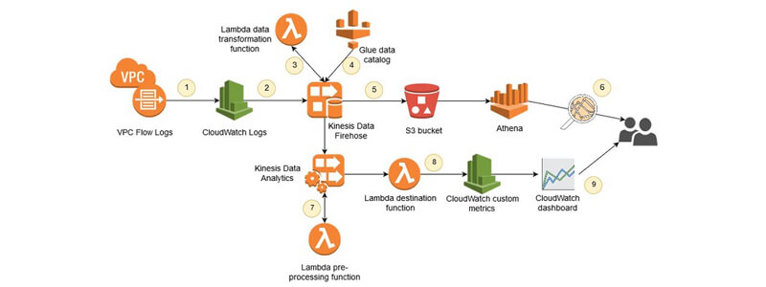
The Amazon VPC Network Access Analyzer is a new tool from AWS that allows customers to identify setups that could result in unauthorized internet connectivity.
In a blog post, AWS stated, "It will point out methods that you may strengthen your security posture while still allowing you and your business to be agile and flexible." "Unlike manual network configuration testing, which is error-prone and difficult to scale, this tool allows you to examine AWS networks of any volume and scale."
AWS Greengrass IoT management
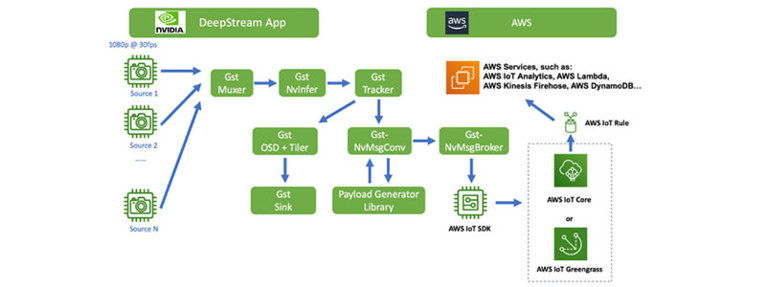
IoT Greengrass is an Amazon Web Services cloud service for developing, deploying, and managing IoT device software and apps. AWS unveiled a new feature for secure control of IoT Greengrass nodes via AWS Systems Manager at re: Invent (SSM).
In a blog post, AWS stated that "managing massive fleets of varied systems and apps remotely can be a difficulty for administrators of edge devices."
As a result, IoT Greengrass and SSM have been merged "to improve the operation and oversight of system software for edge devices," according to the blog post. "Edge device managers may now remotely access and securely manage the multiplicity of devices they own, from OS upgrading to application installations, using the AWS IoT Greengrass Client Software." Additionally, routine maintenance activities for edge compute devices can be automated without the need for extra proprietary operations."
Secure Access to sensitive data
With the addition of row- and cell-level security aspects, AWS launched new features for allowing secure access to sensitive information in the AWS Lake Formation data lake service.
AWS Lake Formation allows users to aggregate and classify data from databases and object storage, but users must decide how to safeguard access to various slices of data.
Row- and cell-level security features for Lake Formation are now generally accessible, according to Selipsky, who spoke at re: Invent.
Users traditionally had to build and manage several copies of data, keep all the copies in sync, and manage "complicated" data pipelines to acquire customized access to slices of data, according to Selipsky.
"Now you can apply access limits for particular rows and cells," Selipsky added of the new changes.
What’s New for the Developers
New SDK and CDK
The initial preview of several new AWS SDKs for the Swift, Kotlin, and Rust programming languages was one statement that attracted the interest of developers. As the programming language gains momentum, the Rust SDK will be in the spotlight. “I am really excited to finally have a Rust SDK because I have seen immense attention in Rust,” Vogels said. Weeks ago, AWS released the AWS Cloud Development Kit Version 2 (CDK), which includes a Construct Hub for easy sharing of open-source construct frameworks.
New Graviton, Titanium, and Mac Instances
Particular developers will be eager to try out some of AWS's new EC2 instance types, which all guarantee a substantial price-to-performance improvement over prior generations of server processors.
The C7g, a new EC2 instance backed by Graviton3, the newest generation of its Arm-based custom silicon array, was the most prominent of them. For computing tasks, these promise to be 25% quicker on average, and even better for specialized cryptography or machine learning applications.
Another instance, Trn1, was released in beta and is the first to use the Trainium chip, which was disclosed last year. Trn1 guarantees better performance for compute-intensive machine learning training applications, with a network bandwidth capacity of 800 Gbps.
AWS Open source Carpenter
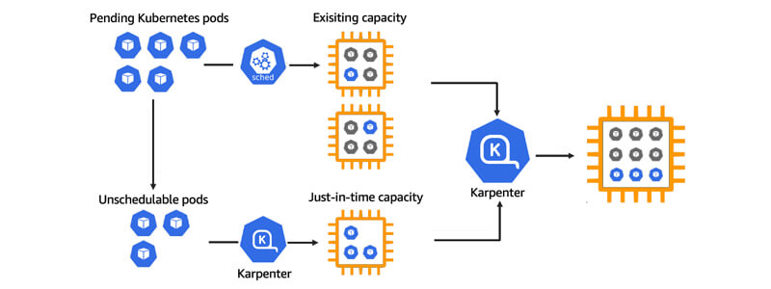
AWS launched the open-source of Karpenter, a Kubernetes cluster autoscaling tool. Karpenter was created to help programmers avoid manual cluster right-sizing by providing "just-in-time compute supply to cover your application's necessities and will soon instantaneously improve a cluster's compute resource footprint to achieve cost performance," according to the company's principal developer advocate.
Royex with AWS
Royex Technologies, a partner of Amazon Web Services (AWS), manages and implements enterprise web and app platforms on the AWS cloud. With the help of our AWS-certified network architects, royex makes it easy for clients to protect sensitive data with a tailored security and threat mitigation policy. We also assist our clients in developing cloud strategies, developing practical migration plans, designing and building cloud environments, as well as facilitating day-to-day cloud operations and management.
Royex Technologies is one of the leading companies in Dubai for designing cloud servers and maintenance. For all AWS consulting and services, choose Royex. To get started, call for any inquiries at +971566027916 or mail at info@royex.net





